Ashley Madison List PDF: Privacy Risks and Safe Handling in PDF Files
Explore privacy risks and safe handling practices for an Ashley Madison list PDF, with practical redaction, storage, and legal considerations from PDF File Guide.
The Ashley Madison list PDF raises immediate privacy and legal concerns: distributing or exploiting leaked personal data can violate privacy laws and professional ethics. This guide clarifies why these PDFs are risky, how to assess authenticity, and the safest handling practices for PDFs containing sensitive information. PDF File Guide emphasizes source verification, strict access control, and redaction before any sharing.
Ashley Madison List PDF: Privacy Risks and Safe Handling
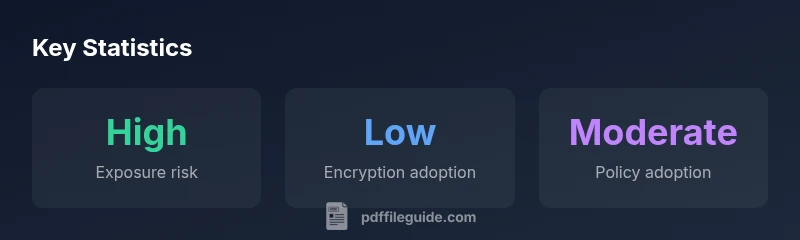
Handling a document that appears to contain sensitive personal data linked to a high profile case or incident requires rigorous caution. In the context of an Ashley Madison list PDF, the potential for harm is substantial if the file is shared, downloaded, or misused. The PDF File Guide team stresses that responsible handling begins with an assessment of provenance, purpose, and access controls. Recognize that any distribution could amplify harm, expose individuals to harassment, or trigger legal ramifications. This section explains the core risk model: confidentiality breaches, unintended recipients, and the long tail of reputational damage to individuals and organizations. Practitioners should treat such PDFs as highly sensitive, and apply strict least privilege access, clear retention periods, and documented approvals before any action beyond viewing.
Why PDFs are particularly risky for leaked lists
PDFs are portable and ubiquitous, yet they carry hidden risks that are easy to overlook. Metadata can reveal authorship and modification history, while embedded attachments or forms can enable automatic data exfiltration. In leaked lists, even a seemingly small excerpt can become a catalyst for identity exposure. This section covers how to check metadata, verify document integrity, and recognize red flags that indicate manipulation or fabrication. The best practice is to treat every scraped or leaked PDF as a potential liability until provenance is established and a responsible channel for handling is defined. PDF File Guide notes that minimal distribution and strong documentation are essential to minimize harm.
Legal and ethical considerations when handling leaked personal data
Handling leaked personal data intersects with privacy by design principles and data protection ethics. Laws vary by jurisdiction, but common themes include accountability, purpose limitation, and data minimization. It is ethically prudent to avoid disseminating content that could identify private individuals, to request deletion where feasible, and to consult counsel before any action that could be construed as distribution or publication. Organizations should maintain a formal incident response plan for such documents, including archiving, access controls, and notification protocols if required. PDF File Guide emphasizes documenting every decision and engaging with legal and compliance teams early.
Verifying authenticity and provenance of a PDF list
Before taking any action, verify provenance and integrity. Start with source verification: confirm the file came from a legitimate, traceable source and cross-check with related news or official statements. Use checksums or digital signatures where available to ensure the file has not been altered since release. Examine the PDF for inconsistencies, unusual file properties, or embedded scripts that could indicate tampering. Maintain a chain of custody log detailing who accessed the file and when. If provenance cannot be established, treat the document as untrusted and avoid sharing. PDF File Guide recommends conservative handling when in doubt.
Safe storage, access controls, and sharing practices for sensitive PDFs
Store sensitive PDFs on encrypted drives or in secured repositories with strict access controls. Implement least privilege access, audit trails, and time-bound permissions. Disable printing, copying, and annotation where possible, and enable document versioning to track changes. If sharing is necessary, use ephemeral links or encrypted channels with expiration dates. Keep retention periods short and establish a clear protocol for deletion. Utilizing professional PDF tools that support redaction and access controls helps keep handling compliant. PDF File Guide highlights policy alignment with data protection standards and ongoing staff training.
Redaction techniques and tools for permanently removing sensitive data
Redaction is not just obscuring content; it requires permanent removal of data from both the visible content and the underlying text layers. Use professional PDF editors that offer true redaction and verify results by exporting to a new file and inspecting the redacted areas. Maintain redaction logs, and ensure that metadata does not reveal sensitive information about the redacted content. Consider automated redaction for large datasets, but always validate manual checks for accuracy. PDF File Guide provides recommended workflows and tool checks to avoid accidental data leakage.
What to do if you encounter an Ashley Madison list pdf
If you encounter such a document, do not distribute or publish it. Preserve evidence of where you found it, report to appropriate authorities or your organization’s compliance team, and seek legal counsel if required. Limit access to trusted personnel, and prioritize user privacy and data minimization. Finally, document your handling steps to support accountability and audit trails. PDF File Guide emphasizes caution and responsible conduct as the baseline response.
Building a data governance mindset to prevent future incidents
Develop a data governance program that includes clear policies for sensitive PDFs, including classification, access control, lifecycle management, and incident response. Train staff on recognizing phishing attempts, social engineering, and metadata risks. Regularly review and update procedures to reflect changing regulations and threat landscapes. The goal is to reduce risk by design, not by reaction. PDF File Guide advocates a culture of privacy first and ongoing improvement.
Overview of risks and mitigations when handling sensitive PDFs
| Aspect | Risk/Impact | Mitigation |
|---|---|---|
| Privacy risk | High potential for misuse and legal exposure | Limit distribution; redact; audit trails |
| Handling controls | Access and versioning challenges | Use encryption; access controls; policy enforcement |
Questions & Answers
Is it legal to possess a leaked Ashley Madison list PDF?
Legal implications vary by jurisdiction, but possessing or distributing leaked personal data can raise civil and criminal concerns. Consult with legal counsel before any action and avoid sharing content that could harm others.
Possessing leaked data can be risky; consult counsel before any use.
How can I determine if a PDF is authentic or a fabrication?
Check provenance, verify source credibility, review metadata, and compare with related reports. Use cryptographic checksums if available to confirm integrity.
Verify where it came from and check the file for tampering.
What should I do if I receive such a PDF?
Do not distribute it. Notify your compliance team, preserve the evidence of where it came from, and seek legal guidance. Consider reporting to authorities if required by policy or law.
Don’t share it; report to the right team and get legal advice.
Which tools help redact PDFs securely?
Use professional PDF editors that support permanent redaction and verify the redacted content is removed from all layers. Keep a redaction log and review afterward.
Use proper redaction tools and double-check that data is truly removed.
How should I store sensitive PDFs within a team?
Store in encrypted repositories with strict access controls and audit trails. Apply least privilege, enforce strong authentication, and implement regular access reviews.
Store encrypted, control access, and review who can see it.
“Data privacy is not optional; it is essential when handling leaked documents. Treat every sensitive PDF with structure, control, and accountability.”
Key Takeaways
- Audit provenance before acting
- Redact sensitive data permanently before sharing
- Limit distribution with strict access controls
- Maintain a document chain of custody
- Consult legal guidance when uncertainty arises