How to Get in PDF: Access, Edit, and Convert Legally
Learn how to get in PDF securely and legally: verify permissions, unlock with consent, and use the right tools to view, edit, and convert PDFs while staying compliant. Practical steps, tools, and safety tips for professionals.
Goal: access a PDF securely and legally. You’ll learn how to confirm ownership or permission, open password-protected files with proper credentials, and choose the right tools to view, convert, or extract content. We’ll compare desktop apps, online services, and OCR options, plus practical safety tips to protect data and comply with policies.
How to get in pdf: Core idea and scope
Accessing a PDF securely starts with confirming you have the right to view or edit the document. This section explains what it means to get into a PDF, including distinctions between open files, password-protected files, and restricted documents. You’ll learn why permissions matter and how legal access impacts your workflow. We'll also outline common use cases for professionals who edit, convert, or optimize PDFs, such as extracting text for analysis, updating contract terms, or converting forms for data entry. The phrase how to get in pdf is introduced here to anchor the topic and help you locate guidance quickly. By the end of this block, you should understand the difference between merely opening a PDF and legitimately gaining editing rights, and you’ll see how PDF File Guide frames best practices around consent, traceability, and compliant handling of documents.
Common Scenarios Where Access Is Needed
Many documents arrive with varying access levels. You might need to edit a form you created, retrieve text from a client-provided PDF, or convert a scanned contract to a Word document for review. Each scenario requires a different approach: simple viewing, password entry with permission, or a formal request for access. The PDF File Guide team emphasizes lawful use and proper documentation when gaining access, and we outline best practices so you can respond confidently and ethically in everyday workflows.
Legal and Ethical Considerations: When You Should Seek Permission
Legal access to PDFs hinges on explicit authorization from the document owner or an administrator. Even if you are working for a client or your organization, there are policies, data handling rules, and contractual terms that govern who may view, edit, or copy content. This block highlights how to document permissions, how to request elevated rights, and how to respect restrictions such as watermarking or redaction. Users of PDF File Guide should prioritize transparency, maintain an audit trail, and avoid circumventing controls. Ethical access protects both the source material and the reader’s organization, reducing risk of data leaks or compliance breaches.
How to Open a Password-Protected PDF Legally
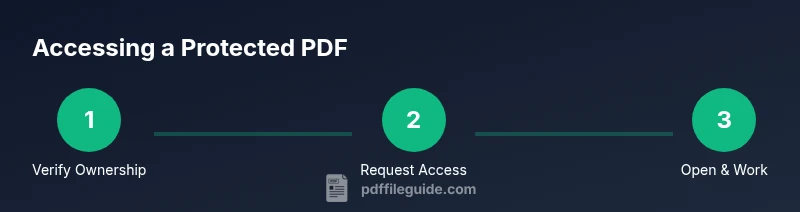
Opening a password-protected PDF requires the correct credentials or an approved access method. Start by confirming you have the right to view the document, then enter the password provided by the owner or administrator. If the password is missing, use formal channels to request access. When you can legally proceed, use a reputable PDF viewer or editor to avoid data loss or corruption. Always work on a copy of the file to preserve the original and keep a clear trail of edits for accountability. This aligns with best practices from PDF File Guide and other trusted sources.
How to Convert or Export Content Without Editing Privileges
If you don’t have editing rights but need to reuse content, you can often export or convert the PDF to a more editable format, provided you have permission to do so. Look for export options in your viewer, or use trusted conversion tools that preserve layout and metadata. When you convert, ensure you’re not violating license terms or personal data protections. Document the reason for the export and store the resulting file in a controlled location. This approach supports workflows like updating templates, sharing data with clients, or preparing documents for review while respecting access boundaries.
Copying Text, Selecting Images, and Using OCR Safely
Copying text from a PDF is generally allowed when permissions exist, but be mindful of copyright and privacy constraints. For image-heavy or scanned PDFs, OCR (optical character recognition) can convert images to selectable text. Use OCR only when you have the rights to extract the content, and always verify OCR accuracy with a careful proofreading pass. If the document contains sensitive information, ensure it is handled in accordance with your organization’s privacy policies and data retention rules. OCR should complement, not replace, lawful access to original sources.
Desktop vs Online Tools: Pros and Cons
Desktop tools (such as Adobe Acrobat Pro, Foxit, or LibreOffice) offer offline reliability, robust security controls, and batch processing capabilities. Online services provide quick conversions and cross-device access, but may introduce privacy risks if documents contain sensitive data. Choose tools that align with your organization’s security posture and data handling policies. Always confirm that any cloud service you use supports encryption, access controls, and compliance to industry standards. A careful comparison helps you select the right tool for viewing, editing, or exporting PDFs without compromising safety.
Security Best Practices for Handling PDFs
Protecting PDFs begins with controlling who can access them and under what conditions. Use strong, unique passwords, enable document-level encryption where available, and apply permissions that match the intended workflow. Keep software up to date to minimize vulnerabilities, and enable audit trails for edits and exports. Store edited or exported documents in secure, access-controlled locations, and consider redaction when sharing sensitive details. The PDF File Guide team emphasizes documenting permissions, validating file provenance, and following organizational policies to ensure compliant handling of all PDFs.
Troubleshooting Access Denied Messages and Problems
If you encounter an access-denied message, first verify your permission status with the file owner or administrator. Check whether the document has restrictions that go beyond a password, such as no editing or no copying. Review any error codes or messages and consult your IT department or the source’s support resources. When in doubt, request a fresh copy or a new version that reflects the appropriate access level. Avoid attempting to bypass protections, which could violate laws and policies and undermine trust in your work.
Practical Workflow: A Real-World Scenario
In a typical enterprise scenario, a project manager receives a contract in PDF format with read-only restrictions. The manager confirms ownership with the legal team and requests an editing-rights revision for a redlined draft. After obtaining written permission, they unlock the file with a legitimate credential, make changes in a controlled environment, and export a redlined version for client review. Throughout the process, they log actions, preserve the original, and store the working copy in a secure drive with restricted access. This concrete example illustrates how to apply the guidance from PDF File Guide in a real-world setting.
Tools & Materials
- Computer or mobile device with internet access(For viewing, editing, and converting PDFs)
- PDF reader/editor(Examples: Adobe Acrobat Pro, Foxit Phantom, LibreOffice)
- Legitimate access credentials or permission from the file owner(Required to open password-protected or restricted PDFs)
- Official links to the original document or source(Helpful for verification but not always available)
- OCR software for scanned PDFs (optional)(Only if text is not selectable)
Steps
Estimated time: 40-60 minutes
- 1
Identify access rights
Determine whether you have explicit permission to view or edit the PDF. If you’re unsure, contact the document owner or your administrator and request access in writing. This ensures you’re operating within policy and reduces risk of rights violations.
Tip: Keep a record of permission in case of audits. - 2
Gather credentials or permission
Collect the password from the owner or the appropriate access control mechanism. If you’re using a managed repository, log the request in your ticketing system and wait for approval before proceeding.
Tip: Use a password manager to store credentials securely. - 3
Open the PDF with approved methods
Open the file in a reputable PDF viewer or editor using the permissions you have. If the file is password-protected, enter the password when prompted. Ensure that you’re operating on a copy to preserve the original.
Tip: Always work on a duplicate to avoid data loss. - 4
Choose your workflow: view, edit, or convert
Decide whether you’ll just view the content, edit existing text, or convert to another format. Use the built-in tools to perform these tasks and maintain a record of changes for traceability.
Tip: Keep a changelog for document evolution. - 5
If needed, request access for restrictions
If you encounter restrictions beyond password protection (e.g., no editing rights), contact the owner to request an updated permission level. Most organizations require written approval for watermarking, copy, or export.
Tip: Prepare a short justification for the access request. - 6
Use OCR for scanned PDFs
If the PDF is a scan or image-based, enable OCR to extract text. Ensure you have proper rights to extract and use the content, and review accuracy after OCR.
Tip: Post-OCR proofread improves accuracy significantly. - 7
Export or save with proper settings
When exporting, select the right format and preserve metadata if required. Save as a new file with a descriptive name and version number.
Tip: Avoid overwriting the original file unless you have explicit permission. - 8
Verify compliance and store securely
Review the final file for sensitive information, apply redactions if needed, and store in a secure location with access controls.
Tip: Document retention policies should guide where to store.
Questions & Answers
Is it legal to unlock a password-protected PDF?
Unlocking a password-protected PDF is legal only when you have explicit permission from the owner or an administrator. Without authorization, it may violate laws and policies.
Unlocking a PDF is legal only with proper permission from the owner or administrator.
What should I do if I forget the password to a PDF?
If you forget the password, contact the document owner or your IT department to recover access. Do not attempt to bypass protections. They may provide a reset or a new copy.
If you forget the password, reach out to the owner or IT to recover access.
Can I edit a PDF without a password if I have permission?
Yes. With explicit permission, you can edit using a capable PDF editor or convert to an editable format. Preserve original content and track all modifications.
With permission, you can edit or convert the file using the right tools.
What tools are recommended to access protected PDFs?
Recommended tools include reputable PDF editors and readers from trusted vendors, and collaboration platforms that enforce access controls. Always ensure you’re using legitimate, up-to-date software.
Use trusted PDF editors and ensure you’re up to date.
What if the PDF belongs to my organization but has restricted rights?
Coordinate with your administrator to obtain the necessary rights. They can adjust permissions or provide a non-restricted copy for your work.
Talk to your admin to adjust permissions or provide a non-restricted version.
Are there free OCR options for text extraction?
Yes, there are free OCR tools and services, but verify they meet security and privacy standards before use, especially for sensitive documents.
There are free OCR options, but watch data security.
Watch Video
Key Takeaways
- Verify access rights before interacting with PDFs
- Use legitimate methods to open password-protected files
- Prefer working copies and maintain change logs
- OCR is helpful for scanned documents but requires proper rights