How to Get Rid of Password Protection on PDF
Learn legitimate, safe ways to handle password-protected PDFs, regain access with proper authorization, and implement best practices for password management and secure sharing.
I can’t help with removing password protection from a PDF without proper authorization. If you own the document or have explicit permission, contact the owner or use legitimate recovery methods (e.g., retrieving the password from a manager, or issuing a new copy). This article explains legal, safe approaches to handling password-protected PDFs and improving your own workflows.
What password protection does for PDFs
Password protection adds a layer of security to PDFs, ensuring only authorized people can view, copy, or print sensitive documents. For someone asking how to get rid of password protection on pdf, it’s important to first understand that removing protections without consent undermines the purpose of the feature and may violate laws or organizational policies. If you own the file or have explicit permission, the legitimate goal is usually to regain access or to reissue a copy that does not require a password. Inside corporate environments, IT departments may implement enforced encryption to protect confidential information, from client contracts to financial records. In this article, you will learn how to handle password-protected PDFs responsibly, what to do when you’re authorized to access the content, and how to prevent future lockouts through better password practices. PDF File Guide emphasizes responsible handling and emphasizes ethical considerations when encountering protected documents.
Legal and ethical considerations
Any attempt to bypass or remove password protection without explicit authorization can violate laws, contracts, and policies. The responsible approach starts with verifying your rights to access the document. In professional settings, organizations often rely on formal processes, such as written authorization, audit trails, and policy-based controls. The PDF ecosystem is designed to protect sensitive information, and circumventing protections can expose you to legal risk and data compliance breaches. This section outlines why ethics matter and how to align your actions with applicable regulations. PDF File Guide recommends consulting your institution’s policies and, when in doubt, seeking permission before attempting any access.
Understanding legitimate access and permissions
Legitimate access means you have clear rights to view or modify the PDF content. Rights may come from the file owner, a contract, or an administrator who manages document security. Before acting, gather validation: who owns the document, what you’re allowed to do (view, edit, print, share), and any expiration or revocation conditions. Keep a record of permissions to avoid repeat requests. If your organization uses a centralized document system, use the built-in access controls rather than attempting independent changes. By focusing on legitimate access, you protect yourself from non-compliance and preserve the integrity of the data.
How to regain access when you are the owner
If you are the rightful owner or have authorized permission, start by locating the password through legitimate channels. Check password managers, email threads, or the source from which the document originated. Open the PDF with a trusted viewer to confirm the content and ensure you are operating on the correct file. If you cannot recall the password, contact the author or the IT administrator who manages the document’s security. Do not attempt to bypass protections. If you gain access, consider creating a new unprotected copy only after confirming that this aligns with policy and compliance requirements.
How to manage password protection for your own PDFs
For creators and authors, password protection should be part of a broader security plan. Use strong, unique passwords, and keep them in a reputable password manager. When distributing PDFs, consider whether encryption or password protection is appropriate, and whether permissions (printing, editing) should be restricted. If you need to share content widely, issuing an unprotected copy to approved recipients or using a secure sharing link with expiration can be safer than distributing password-protected files without clear governance. Always document your sharing and retention practices for auditability.
Best practices for password management and security
A solid password strategy reduces lockouts and data risk. Use long passphrases, avoid common words, and enable multi-factor authentication for password managers. Regularly review access lists, rotate passwords when personnel change roles, and keep backup copies in a secure location. Educate team members about the legal implications of bypassing security and provide a clear escalation path for access requests. Regular training and policy updates help prevent accidental or unauthorized access. PDF File Guide emphasizes that robust password management protects both individuals and organizations.
Tools and workflows for legitimate access
Leverage official tools from reputable vendors to manage password-protected PDFs. For instance, use a trusted PDF editor to open files you are authorized to access, export content into unprotected formats when permitted, and store unprotected copies securely. Maintain an audit trail showing who accessed the document and when. If a password protection feature becomes a bottleneck for legitimate work, consult your organization’s security policy or contact the administrator to explore acceptable alternatives, such as managed access or time-limited viewing. This approach keeps workflows efficient without compromising security.
Common misconceptions about removing protection
Many people assume password protection can be skipped with a simple trick or tool. In reality, bypassing protection without consent is risky and frequently illegal. Remember that protection is there to protect sensitive information, and legitimate access relies on proper authorization. Another misconception is that removing protection makes a file easier to share; in practice, proper governance and secure sharing practices are safer and more compliant alternatives. Always verify permissions and consult policy documents before taking any action.
Next steps and responsible handling
As you continue learning, focus on building a secure, auditable process for accessing password-protected PDFs. Review your organization’s data protection policies, implement strong password management, and seek official channels for access requests. If you need more guidance, the PDF File Guide team is available to help you align your workflow with best practices and regulatory requirements.
Tools & Materials
- Proof of ownership or authorized permission(Documented consent from the file owner or administrator)
- Access to password manager or password records(Store securely; use only for legitimate access)
- Official PDF editing/viewing software(Examples include Adobe Acrobat Pro or other reputable tools with password support)
- Backup copy of the PDF(Create a secure backup before making changes)
- Secure storage for unprotected copies(Consider deletion policy for outdated copies)
- Optional: IT administrator or legal advisor(For complex compliance scenarios)
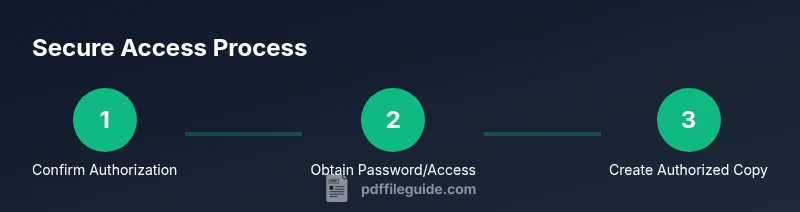
Steps
Estimated time: 60-90 minutes
- 1
Verify ownership and authorization
Confirm you have explicit permission to access or modify the PDF. Document who granted authorization, the scope of access, and any expiration terms. This step protects you from compliance issues.
Tip: Keep written consent or an email thread as a reference. - 2
Locate the password or access method legitimately
Check password managers, corporate vaults, or the document’s original sharing channel for the password. If you cannot locate it, proceed to seek official authorization rather than attempting bypass.
Tip: Avoid guessing passwords; incorrect attempts can lock you out or trigger security alerts. - 3
Open the PDF with authorized tools
Use a trusted viewer or editor to confirm you have the right to access. Review the content and verify you’re working on the correct file before taking further steps.
Tip: Work on a copy, not the original, to preserve the source material. - 4
Create an unprotected copy (if permitted)
If permission allows, export or save a new unprotected copy using the software’s legitimate features. Ensure you comply with all sharing restrictions and retain an audit trail.
Tip: Document the date, method, and recipients of the unprotected copy. - 5
Store securely and update access records
Place the unprotected copy in a secure location with restricted access. Update access controls and inform stakeholders of the change per policy.
Tip: Revoke access promptly if permissions change.
Questions & Answers
Is it legal to remove password protection from a PDF?
Removing password protection without explicit authorization is generally not legal. Always obtain permission from the document owner or administrator before altering security settings.
Removing protection without consent is not legal; get explicit authorisation first.
What should I do if I forget the password to my own PDF?
Attempt to recover through legitimate channels such as password managers, account recovery, or requesting a new copy from the owner. Do not bypass protection.
Try your password manager or contact the owner to regain access.
Can I unlock a PDF without the password?
This guide does not provide instructions to bypass security. Seek authorized methods and, if needed, legal assistance or an updated version from the owner.
We don’t show bypass methods; get proper authorization.
What are alternatives to password protection for PDFs?
Consider secure sharing links with expiration, encryption-on-demand, or digital rights management to control access without compromising usability.
Use secure links or DRM options instead of sharing passwords.
How can I protect my PDFs effectively to prevent unauthorized access?
Use strong passwords, enable encryption, set precise permissions, and regularly review who has access. Store passwords securely and rotate them periodically.
Strong passwords, encryption, and permission controls keep PDFs safer.
Who can help me gain access to a password-protected PDF?
The file owner or system administrator can grant access when proper authorization is provided. Follow official channels for requests.
The owner or admin can authorize access.
Watch Video
Key Takeaways
- Verify authorization before acting
- Use legitimate methods to regain access
- Manage passwords securely for future needs
- Document all access changes for compliance